Organizations standardize and automate their business processes to improve operational efficiency and minimize operational risk. Identification of all possible hazards during the process design stage is usually impossible as processes are executed in complex and changing environments. Moreover, many tasks in business processes are performed by human resources who are prone to mistakes. Process mining techniques can help identify process risks by analyzing process execution data.
Risk can be defined as the “effect of uncertainty on objectives†(ISO Guide 73:2009[i]). Process objectives are typically defined in terms of time, cost, quality, and compliance. Other dimensions of process performance can be considered (e.g., process fairness or flexibility); however, these are usually difficult to quantify. The performance of business processes can be affected by various factors (e.g., uncertainties in supply or demand, equipment malfunctions or human errors) which can lead to process delays, budget overruns or low-quality outputs.
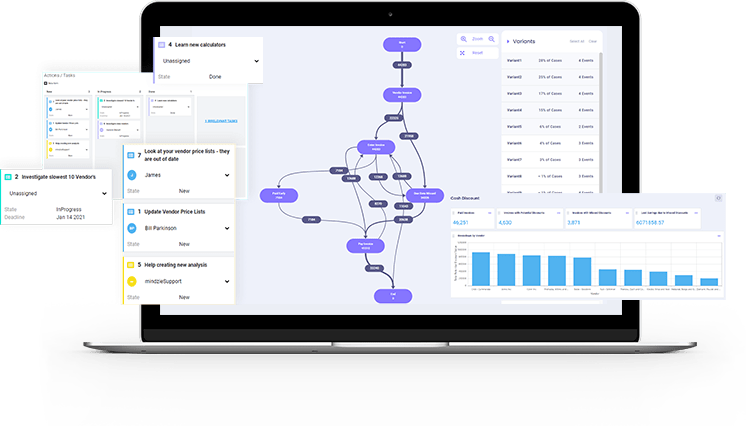
Several process mining methods aim to predict the likelihood that a running process instance will not achieve a certain desired outcome (e.g., Pika et al., 2012[ii]). For example, they can predict that an insurance claim or a loan application will not be processed by the due date, or the processing cost will be too high. These methods typically extract pre-defined process features from process execution data (e.g., an abnormal activity duration, repetition of a process step, or execution of an activity by a certain resource) and use them as input to a machine learning method. Processes are not executed in isolation; their performance can be affected by other processes. For example, if an employee handles a few tasks in several processes, the employee can become a bottleneck in these processes. Some methods consider such inter-process relations (e.g., by checking employee workload). Process risk identification methods do not only identify the likelihood of an undesired process outcome, but they can also provide information that helps to mitigate the identified risk. For example, a risk identification method can notify the process owner that there is an increased likelihood of a low-quality output because a quality check was skipped, and a critical process step was performed abnormally quickly by an inexperienced employee.
Managing risks in individual process instances can be costly. For non-critical processes organizations may choose to tolerate a certain level of risk. For example, instead of receiving notifications about identified risks in individual process instances, the process owner may choose to be notified when the overall process risk reaches some predefined level (e.g., more than 20% of cases are likely to be delayed). Some process mining methods can evaluate the overall process risk and predict its future levels (Pika et al., 2016[iii]).
Once process risks are identified, the process owner can choose an appropriate risk mitigation action (e.g., some activities may be reassigned to employees with a lower workload). Some process risks may trigger process redesign. For example, if there is a high rate of mistakes in an important process step, the process may need to be modified to include a mandatory check by a second employee (“four-eyes principleâ€).
Risk identification is a crucial first step in the risk management process. Process mining techniques can automatically identify risks in running process instances, evaluate the overall risk exposure, and predict future risk levels, thus enabling timely risk mitigation and improving process performance.
Anastasiia Pika, PhD